Improving cyber resilience: the role boards have to play
COVID-19 has led to a surge in the use of digital technologies, an acceleration of organisations’ digital transformation programs and a material increase in cyber risk, both in Australia and overseas. During the 2020-21 financial year, the Australian Cyber Security Centre (ACSC) received 13 per cent more cybercrime reports than in the previous year. Driven by more complex and sophisticated cyber-attacks, the ACSC also classified a higher proportion of cyber security incidents as ‘substantial’ in impact. Against this backdrop, the need for boards’ ongoing due diligence in the cyber area is greater than ever.
APRA’s 2020-2024 Cyber Security Strategy, announced in November 2020, aims to help improve the Australian financial system’s resilience against the ever-growing cyber threat. The strategy consists of a number of focus areas and associated initiatives, and APRA recently completed two pilot initiatives in the strategy: a technology resilience data collection, andan independent assessment of a pilot set of entities’ compliance with CPS 234, APRA’s Information Security Prudential Standard.
The insights gained from the two pilots, and from APRA’s supervisory activities, reinforce APRA’s view that boards need to strengthen their ability to oversee cyber resilience. Ultimately, APRA expects boards to have the same level of confidence in reviewing and challenging information security issues as they do when governing other business issues.
APRA’s technology resilience data collection and CPS 234 independent assessment
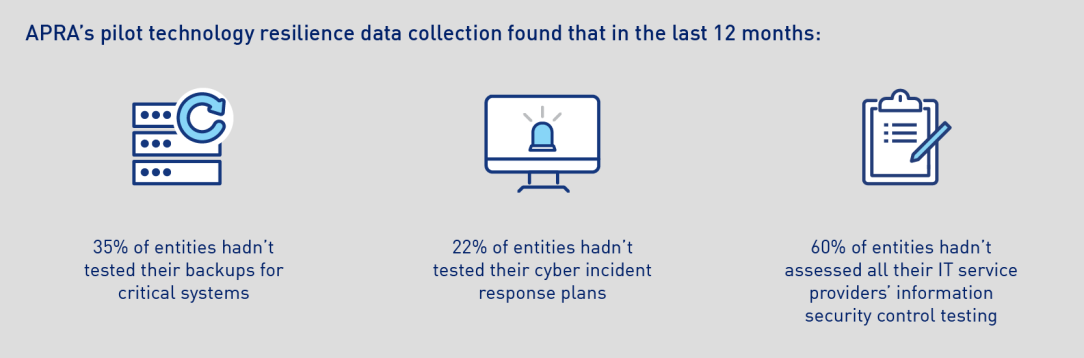
APRA’s pilot technology resilience data collection (the data collection) involved surveying regulated entities across the banking, superannuation and insurance industries on a number of IT and cyber topics, including IT resourcing, system health, information security capabilities, and disaster recovery statistics. The goal of the data collection is to help APRA get a better view of potential IT and cyber control weaknesses across entities, and to share relevant insights with the financial industry.
APRA’s pilot independent CPS 234 tripartite assessment (CPS 234 assessment) involved a small sample of banking, insurance and superannuation entities undergoing an independent assessment against the requirements of CPS 234. This is the initial pilot phase of a broader CPS 234 tripartite assessment exercise, which will be rolled out across all regulated entities with the aim of helping embed the baseline cyber practices required by the standard.
The results of the two pilots, together with the outcomes of recent supervisory activities, led APRA to conclude that boards need to play a more active role in:
- Reviewing and challenging information reported by management on cyber resilience;
- Ensuring their entities can recover from high-impact cyber-attacks (e.g. ransomware); and
- Ensuring information security controls are effective across the supply chain.
1. Reviewing and challenging cyber information
Under CPS 234, boards must ensure their entity maintains information security in a manner commensurate with the size and extent of threats to its information assets (i.e. information and information technology, including software, hardware and data, both soft and hard copy), and which enables the continued sound operation of the entity.
Disappointingly, APRA’s observations from the CPS 234 assessment and its supervisory activities have found little evidence of boards actively reviewing and challenging the information that senior management has provided on cyber topics. In many cases, APRA observed that management reporting on information security to the board is not fit-for-purpose and unlikely to facilitate meaningful discussion. For example, APRA identified that some boards are not receiving information about the effectiveness of testing of information security controls.
APRA expects boards to regularly seek assurance from and, as appropriate, challenge management on the effectiveness of the information security controls. APRA suggests that boards engage with their management team on questions such as:
- What are the information security vulnerabilities and threats faced by our entity?
- Is our entity’s current information security capability sufficient?
- What is the overall health of the entity’s information assets and the information security control environment?
- How much of the information security control environment is regularly tested?
- What are the most severe but plausible security compromise scenarios that management considers the entity cannot currently withstand?
Prudential Practice Guide CPG 234 also provides further guidance on the types of information that management can provide to support their board’s oversight of information security, including:
- regular updates of key initiatives from the entity’s information security strategy,
- incident trend analysis and test results of incident response plans,
- progress on the remediation of gaps identified in the entity’s information security controls, and
- educational materials to help increase boards’ awareness and knowledge of information security.
2. Ensuring recovery from high-impact cyber attacks
Another area that requires board focus is their entity’s ability to recover from major cyber-attacks. According to responses to the data collection, more than one third of respondents have not tested their backups for critical systems in the past 12 months. And 22 per cent of entities in the data collection have not tested their cyber incident response plans in the past 12 months. This is concerning as these entities may find themselves unable to recover critical data in the event of a high-impact cyber compromise such as a ransomware attack, leading to prolonged, and possibly severe, business disruption.
As part of its supervisory activities, APRA will continue to ensure entities can adequately protect themselves in high-impact disruption scenarios, and encourages boards to regularly seek assurance in this area by communicating with management on questions such as:
- What backup and recovery testing has been conducted for critical information assets, and is the testing coverage sufficient?
- What plausible disruption scenarios have been considered and tested to ensure the backup and recovery capability is effective – including recovery from a successful ransomware attack where protection of backups is key?
3. Ensuring effectiveness of information security control across the supply chain
Under CPS 234, an APRA-regulated entity must test the effectiveness of its information security controls through a systematic testing program. Where the entity’s information assets are managed by a service provider (i.e. a related or third party), it must ensure that the relevant information security controls are appropriately tested based on the rate of change in vulnerabilities and threats, and the materiality and changes of the information assets.
However, results from the CPS 234 assessment and APRA’s supervisory reviews show that entities are not applying sufficient rigour in testing the design and operating effectiveness of their service providers’ information security controls. Testing coverage may also be an issue, as the data collection found that over the past 12 months, 60 percent of entities had not managed to assess all of their IT service providers’ information security control testing as per the requirements of CPS 234. APRA also observed that some entities relied heavily on control self-assessments or surveys completed by their service providers, and had not taken any steps to independently verify that the information security controls were effective.
Given cyber-attacks are increasingly targeting suppliers in order to find that ‘weak link’, the need for improvement in this area is critical. APRA encourages boards to play a more active role in challenging management’s assumptions regarding the effectiveness of service provider information security controls by asking questions such as:
- What controls are in place to protect our business and minimise customer impact when the information security of one (or more) of our suppliers is compromised?
- What blind spots do we have on the end-to-end supply chain of our business which could challenge our resilience to a cyber-attack?
Looking ahead
As the peak governing body of an entity, boards play a vital role in directing all entity-related activities, including those involving cyber security. It is ultimately the board’s responsibility to ensure that management is fully across the cyber threat they face and, where necessary, takes appropriate action to ensure its entity remains cyber resilient.
Over the next couple of years, APRA will continue to roll out the CPS 234 independent assessment process for the remaining entities across the banking, superannuation and insurance industries. APRA intends to share relevant insights with industry from its data collection and other strategic initiatives on cyber security, with a view to lifting practices and enhancing cyber resilience throughout the financial sector.
Media enquiries
Contact APRA Media Unit, on +61 2 9210 3636
All other enquiries
For more information contact APRA on 1300 558 849.
The Australian Prudential Regulation Authority (APRA) is the prudential regulator of the financial services industry. It oversees banks, mutuals, general insurance and reinsurance companies, life insurance, private health insurers, friendly societies, and most members of the superannuation industry. APRA currently supervises institutions holding $9.8 trillion in assets for Australian depositors, policyholders and superannuation fund members.